Take back 80% of your time with smart payroll software
Enjoy effortless, accurate and stress-free payroll with cloud-based software that scales with your business.
16,000+ small and medium businesses trust PayFit
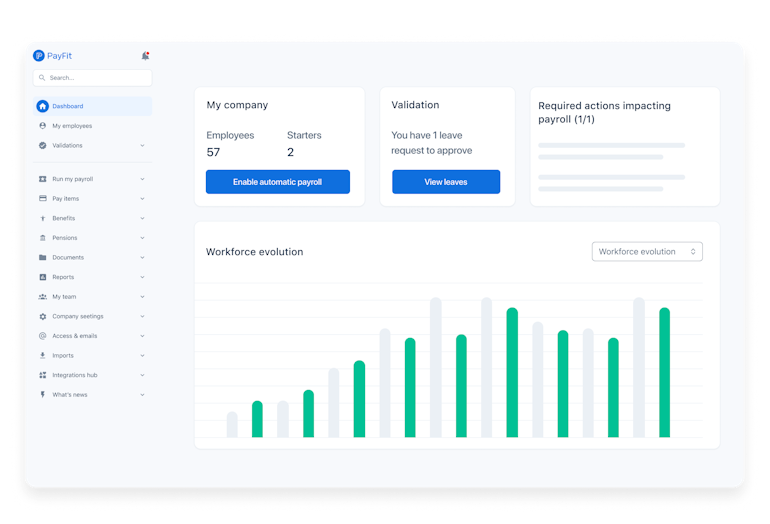
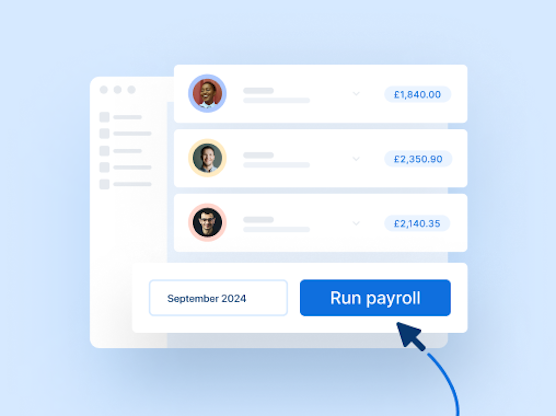
Manage and pay your people in just a few clicks
Leave spreadsheets and tedious calculations in the past. Say ‘yes’ to cloud-based payroll software that automates payments, HMRC submissions, P11ds and more.
Automated
We’ve taken the ‘complicated’ out of payroll. User-friendly workflows automate up to 90% of manual payroll tasks.
Real-time
With PayFit, any change is instant. Make salary changes or modify pay variables, and watch payslips update in real time.
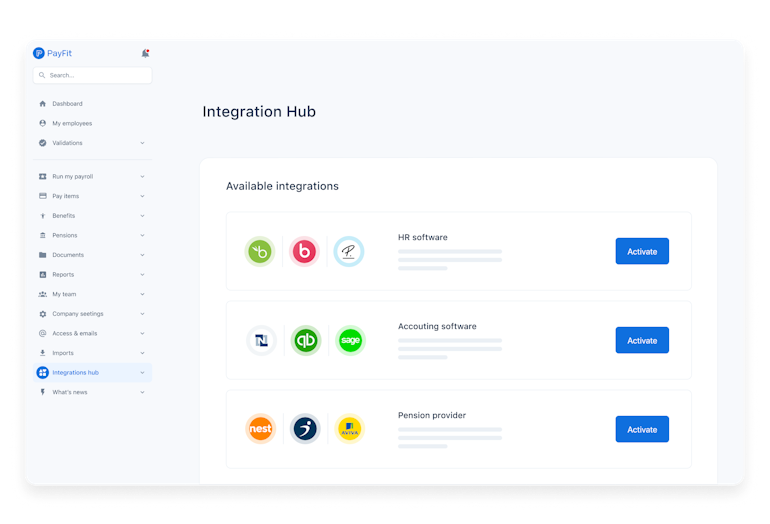
Integrated
Experience best-in-class integrations with leading HRIS like Personio and BambooHR so you can share data more seamlessly.
Integrate payroll & HR
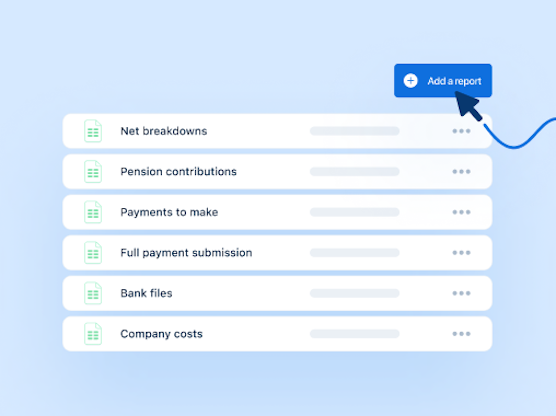
Salary changes. Deduction calculations. Pension and RTI submissions. If it’s payroll-related, we’ve automated it.
No more double data entry. From accounting and HR software to leading pension providers, we sync with solutions across the board.
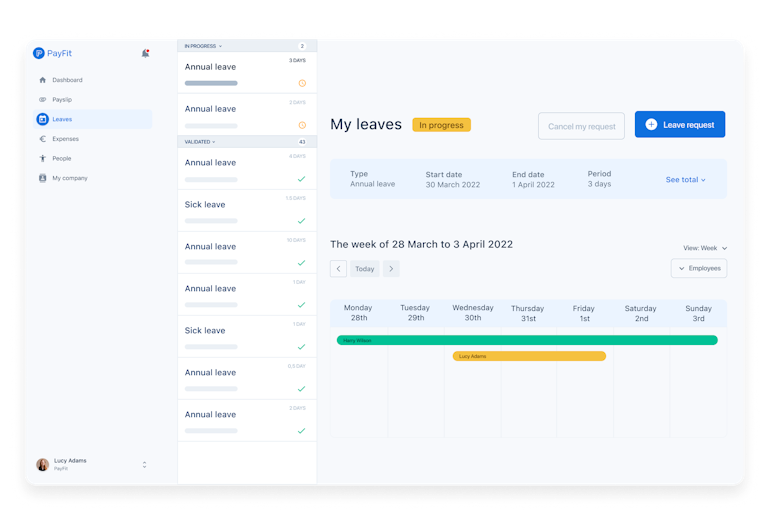
Easily manage leaves & absences. Record sick days and annual leave and watch payslips update in real time.
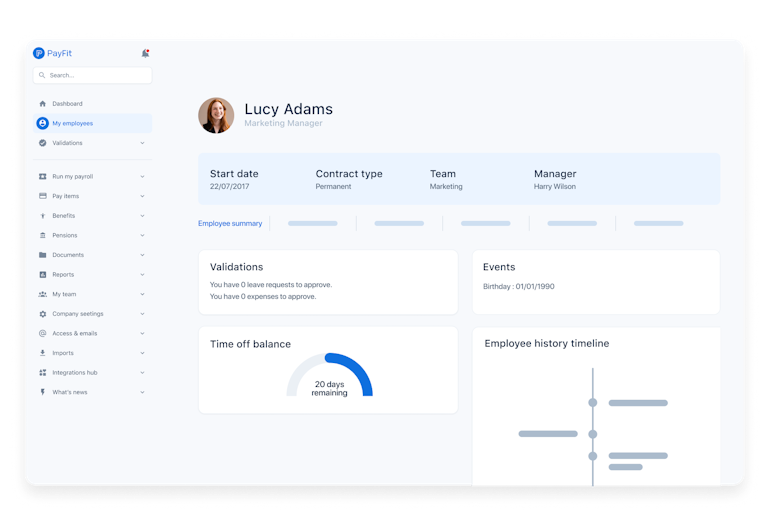
You can also make PayFit your all-in-one HR system. From onboarding to benefits, manage all HR processes in one place.
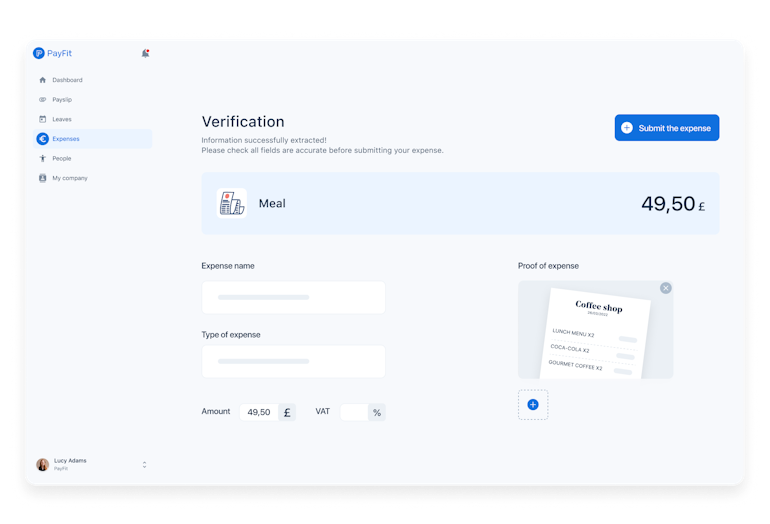
PayFit helps employees manage expenses efficiently. Enter expenses and watch your payslips update in real time.